Category: Articles
-
Manus AI vs. Deepseek: A Comprehensive Comparison of Two Leading AI Platforms
The AI industry is rapidly evolving, and two major players—Manus AI and Deepseek—are at the forefront of this transformation. While both platforms are revolutionizing various sectors with their advanced AI capabilities, they each offer unique approaches to AI development. In this blog, we’ll compare Manus AI and Deepseek to examine their competitive advantages, technological strengths,…
-
Gemini Flash 2.0 vs DALL·E vs MidJourney vs GPT-4V: The Ultimate AI Image Generation Showdown
AI-powered image generation has taken a huge leap forward in 2025 with Google’s Gemini Flash 2.0, competing directly against OpenAI’s DALL·E 3, MidJourney, and GPT-4V. If you’re wondering which AI creates the most realistic, high-quality images, this comparison will help you decide. From ultra-fast image creation to artistic precision, each AI model has its strengths.…
-

How to Use Anthropic MCP Server with Open LLMs, OpenAI, and Google Gemini
What if you could break free from the limitations of traditional AI systems and seamlessly integrate open-source AI with Claude MCP AI, OpenAI, and Google Gemini? The future of AI development has arrived with Anthropic’s MCP, and here’s why it’s about to change everything. In this blog, we’ll dive into Anthropic’s Model Context Protocol (MCP),…
-

Contact Center Automation Trends for 2025 and How Our AI Call Agent is Leading the Way
Artificial intelligence (AI) is transforming how businesses interact with their customers, particularly within contact centers. From automating repetitive tasks to improving customer experience, contact center technology is evolving at an unprecedented pace. Contact Center Automation 2025 by understanding emerging trends, businesses can better equip themselves to meet customer expectations and stay competitive in this fast-changing…
-

IT Infrastructure Management: Building a Robust Digital Backbone
IT infrastructure management serves as the foundation of a company’s success in an increasingly connected world. A well-structured and efficiently managed IT infrastructure ensures seamless operations, strong security, and the ability to scale, allowing businesses to stay competitive and agile in a technologically dynamic environment. This comprehensive guide outlines the core components of IT infrastructure…
-

How AI Will Transform Your Business: A Comprehensive Guide
The AI revolution is here, and it’s changing the way businesses operate, grow, and innovate. From automating workflows to enabling smarter decision-making, AI is reshaping industries and creating new opportunities for success. For businesses aiming to stay ahead, AI isn’t just an advantage—it’s a necessity. At itcompany.ai, we specialize in building AI agents designed to…
-
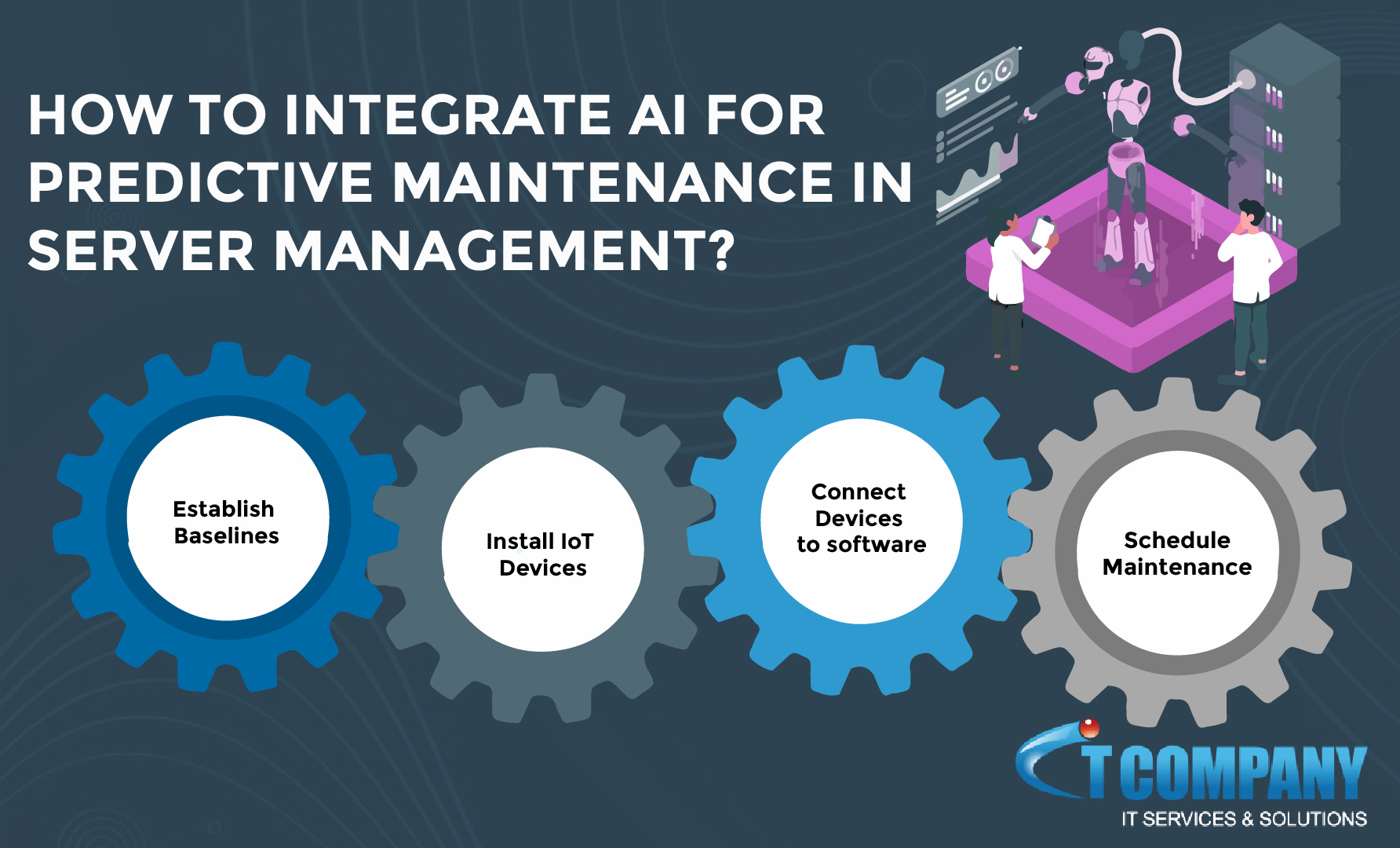
How to Integrate AI for Predictive Maintenance in Server Management
Server management is a critical aspect of any organization’s IT infrastructure. In today’s fast-paced digital world, the ability to predict server issues is crucial for maintaining uptime and reducing operational expenses. This is where the integration of artificial intelligence (AI) and predictive analytics can play a significant role. In this article, we will explore how…
-

How Cybercriminals Exploit GTM to Steal Data
The sun had barely risen when Jane, a small business owner running a boutique online store, opened her laptop to check sales. She had just launched a massive marketing campaign to boost her online presence. However, what she discovered instead was a nightmare. Her checkout pages, designed to capture customer payment details, had been hijacked.…
-

How to Fix Unwanted Indexed URLs
If you’re dealing with unwanted URL indexing in Google, you’re not alone. Many websites face this issue, especially when using dynamic URLs with query parameters, like ?add-to-cart. Google can crawl and index these URLs, even if you don’t want them to show up in search results. The usual advice includes using rel=canonical, robots.txt, or noindex…
-

Battle of AI Competition – The Most Powerful AI Tool
As it is said: “Artificial Intelligence is not a tool of the future—it’s the tool of today, transforming industries, enhancing human capabilities, and solving complex problems.” The most powerful AI tools are driving innovation, combining flexibility, advanced algorithms, and robust performance. From natural language processing to predicting the future, they never miss a beat. Winning…